A partial decomposition of the main system predicate in the intelligent... | Download Scientific Diagram

database - Oracle PL/SQL: Compilation problems with triggers - ORA-00904 errors and invalid identifiers - Stack Overflow
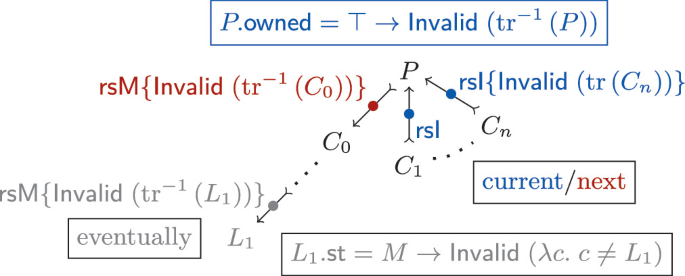
Hemiola: A DSL and Verification Tools to Guide Design and Proof of Hierarchical Cache-Coherence Protocols | SpringerLink

An example of PHP code implementing referential constraint enforcement... | Download Scientific Diagram
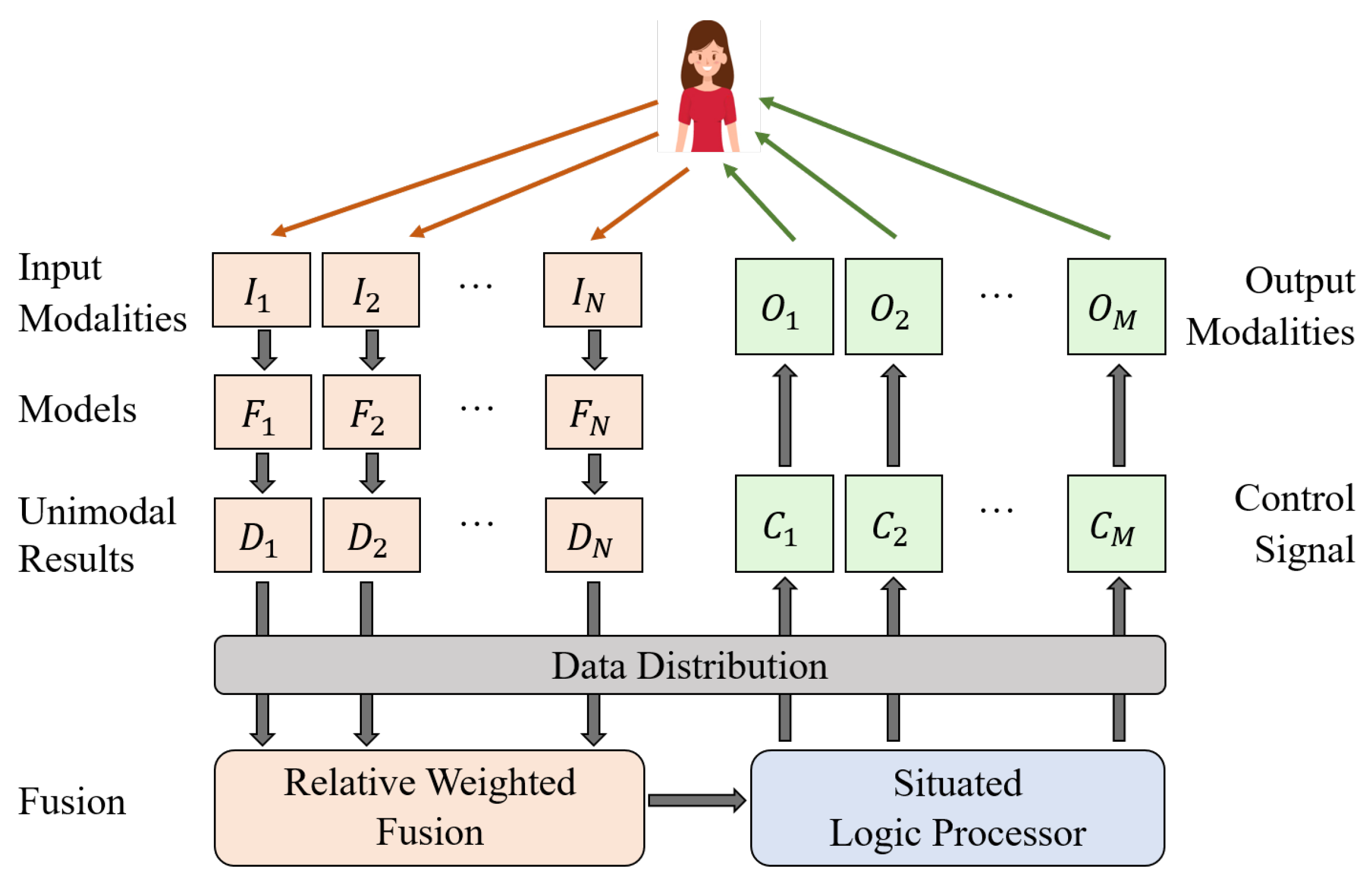
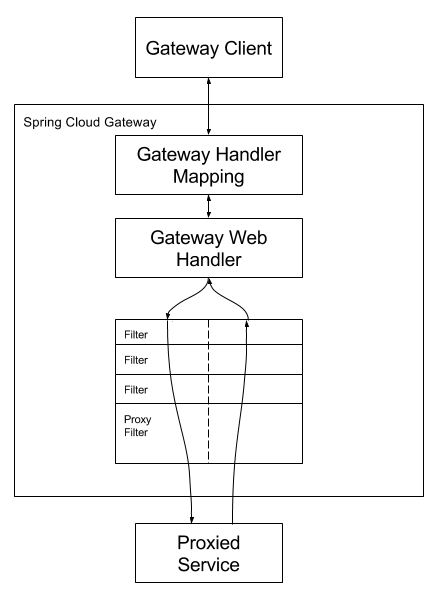
Applied Sciences | Free Full-Text | A Parallel Multimodal Integration Framework and Application for Cake Shopping

OIE4PA: open information extraction for the public administration | Journal of Intelligent Information Systems